Would you like to find out what’s new at BENOCS? Or see what others are saying about BENOCS products? Or perhaps even meet us in person at an industry event?
You’ve come to the right place.
May 21, 2025
1&1 Versatel relies on BENOCS to optimize its fiber optic network
The telecommunications provider 1&1 Versatel, which specializes in enterprise customers, has recently deployed the German technology BENOCS Analytics to monitor traffic flows in its fiber optic network. BENOCS is a specialized provider of network analysis software.
April 10, 2025
Matching routes to traffic levels at EPF 2025
Next week at Global Peering Forum in Denver, Stephan Schroeder will give some insight into identifying asymmetrical traffic, which, if left unremedied, can cause latency and performance issues, load-balancing problems, routing instability and poor quality of service.
April 8, 2025
Global Peering Forum
We are excited to be heading over to Colorado, USA, next week for this year's Global Peering Forum. We are more than excited to announce that we are also first-time sponsors of the event this year!
March 19, 2025
Peering Days – Matching routes to traffice levels
ICYMI: Péter György is heading over to Croatia to attend Peering Days 2025 next week. While there he will present “Forward Path: Matching routes to traffic levels” on Thursday, March 27, just before the lunch break at 12:10pm. Be sure to check it and all the other presentations out! https://lnkd.in/d99t-ffZ
March 18, 2025
Peering Days 2025
Peering Days is coming up next week and Péter György drew the lucky card! From March 25-27 he will be in beautiful Croatia to take part in the 2025 edition of Peering Days. While there he will present “Forward Path: Matching routes to traffic levels” on Thursday, March 27, just before the lunch break at …
March 3, 2025
APAN 59 – Use cases for NRENs
Hot on the heels of this year’s APRICOT, Stephan Schroeder in exchanging the tropics for the more temperate climate of Japan this week. From March 3-7, Stephan is looking forward to connecting with the NREN crowd at APAN 59. While there, he will present some analytics use cases of interest to the community.
February 27, 2025
APAN 59
After APRICOT wraps up this week, Stephan Schroeder will extend his stay in Asia to head up to Japan to attend APAN59 in Yokohama. It’s our first time taking part in APAN, so we are pretty excited about it – it will also be the first time in 10 years that an APAN meeting has …
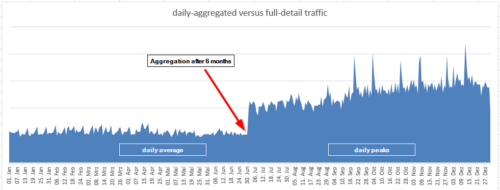
February 19, 2025
How monitoring tools can lead you astray (and why BENOCS won’t)
When monitoring your network traffic, you rely on tools to provide precise, actionable data. But what if some tools “lie” – not out of malice, but due to hidden methodologies that mask the truth? Let’s uncover how certain practices can lead to inaccurate traffic analyses.